Given the acute demand-side stresses that COVID-19 has inflicted upon aviation, cybersecurity concerns may have dropped down on some MRO companies’ agendas. Even so, the threat to IT systems and data has not diminished. In fact, it has probably increased, as the move to remote working and video conferencing affords cybercriminals more vectors to pursue attacks, hacks and malicious snooping.
The need for vigilance was demonstrated in June, when a U.S. subsidiary of ST Engineering—aircraft MRO provider VT San Antonio Aerospace—suffered a serious breach by what it termed “a sophisticated group of cybercriminals.” Known as the Maze group, the perpetrators have attacked numerous industries since 2019, typically stealing company data and threatening to make it public unless a ransom is paid.
Preventing such ransomware attacks has become a priority for IT managers in most sectors, including aviation. SR Technics, for example, regularly conducts risk assessments to identify the measures needed to prevent, detect and thwart a ransomware attack.
“As a result of our most recent risk assessment, which is part of our theme-based information security plan, we made additional security investments in our IT infrastructure [and] employee security awareness and are in the process of engaging our security partner to improve our detection and response services,” says Patrick Kuster, senior vice president of group IT for SR Technics. “We will end this particular theme with a simulation of a ransomware attack to assess the effectiveness of our investments.”
Other parts of the MRO supply chain are similarly worried. “Our biggest concerns are breaches of sensitive information, ransomware and fraud,” says Paul Morales, vice president of information technology for GA Telesis. “These seem to be the most prevalent attacks in most industries, including aviation,” which has driven the MRO to launch “several new initiatives based upon the increased frequency of cyberattack attempts,” he says.
Although the breach at VT San Antonio has been the most well-publicized cyberattack in the MRO sector, Morales reports that GA Telesis has thwarted “several multimillion-dollar fraud attempts,” mostly involving phishing emails, which typically attempt to con sensitive information (such as passwords or bank account details) out of their targets.
Indeed, most of the companies that Inside MRO interviewed about this issue reported some kind of cyber-attack or attempted attack.
“We had one of our servers breached in 2016,” says Max Wooldrik, chief executive of Dutch part-out company APOC Aviation. “However, we noticed this within one business day, and thankfully no damage was done in the interim.”
Dangers and Defenses
While ransomware attacks are essentially blackmail attempts, the aviation aftermarket has more to fear than financial payouts. Keeping client data confidential is a top priority, but manufacturers and MRO providers must also guard against intellectual property theft and other malicious actions by rival companies or even nation states.
“The loss of our corporate data would be devastating,” says Wooldrik. “We have worked very hard to design our own proprietary software and algorithms to be able to identify successful projects and business opportunities. This really sets APOC apart from various competitors and is the driving force behind our success. Obviously, we wouldn’t want this data to fall into the wrong hands.”
Losing customer data is another big danger. As well as the reputational and relationship impact, this presents additional headaches for companies that use such information to provide tailored or predictive MRO services.
For example, Lufthansa Technik has access to certain airline data via its Aviatar platform, although it includes only what each customer is willing to share. As well as keeping each customer’s data separate, the MRO provider uses encryption throughout the Aviatar platform, both for data in storage and in transit. This is the last line of defense if other security measures—such as Aviatar’s firewall and automatic threat detection—are breached.
MRO companies are also becoming more vulnerable as internet-enabled devices and components proliferate on aircraft and in the hangar.
“With almost every new device having a network interface of some sort, the attack surface increases. Because these devices utilize multiple operating systems, your standard ‘agent’ endpoint security software will not suffice,” Morales notes.
To address this issue, GA Telesis uses software that monitors traffic to and from its data center—i.e., to and from the outside world—and traffic among devices within its own internal network. This so-called “North/South, East/West” monitoring “allows us to have a stronger defense to threats missed by traditional signature-based security tools,” Morales says.
Another approach to security is to authorize specialized companies to attempt simulated attacks on an IT system to discover any weaknesses.
“We have conducted various pentests [penetration tests] in the past and will continue to do so,” Wooldrik says. “Fortunately, the outcomes of these tests are usually very positive and show that we have above-standard security measures in place.”
The Human Factor
Although cybersecurity requires a multilayered approach that encompasses firewalls and mail filters as well as antivirus, antimalware and intrusion-detection software, even the most sturdy technological defense is easily undermined by human error or sloppy practice, be it through poor password security, the use of unauthorized devices or an inability to detect scams.
This explains the increasing use of phishing attempts at both the corporate and individual levels. Most data breaches that occur are thought to be the result of human error. “This means the attackers understand that going after the user typically yields a better result than a ‘brute force’ attack,” Morales notes.
All of this means that any effective cybersecurity strategy will rely on recruiting the right IT staff or outside contractors and training the wider workforce to observe proper security practices. “We invest significant time in ensuring that employees know how to identify potential cybersecurity risks and how to correctly respond to them,” Kuster confirms.
Morales agrees, noting that GA Telesis’ best defense is its “human firewall.” To strengthen that wall, “we continue to invest in user training and simulation testing,” he says. “We have found while classroom instruction is effective for security training, conducting ongoing simulation and remediation increases retention of the skills required to spot threats.”
Recruitment
The staffing squeeze faced by the wider MRO sector in recent years seems almost an anachronism given the present tide of mass layoffs and predictions for years of lower demand. However, the crisis has deepened many businesses’ reliance on technology and connectivity, meaning there has been no let-up in demand for IT staff.
“As a result, the technology field remains very competitive, and our teams are often sought after,” says Morales at GA Telesis. High pay aside, he notes that the key to hiring and retaining the right personnel is to keep them engaged, a view echoed by Wooldrik at APOC Aviation in the Netherlands.
“The fact that we are using the latest technologies really helps get people excited about our projects,” Wooldrik says. “Our system is built up using a CQRS architecture. . . . Not a lot of developers are familiar with this technology, but most know that all major websites like Google, Amazon, Facebook, etc., use this architecture to help scale things up. Therefore, most developers are excited to become part of a team where they can master this technology.”
He notes that the aviation industry itself is also a draw, as many people “tend to have a soft spot for aircraft,” which is good news for those aftermarket companies not sporting the network architecture du jour.
Another option is to use a mix of internal and external IT specialists, which is how SR Technics has responded to what Kuster describes as “the general shortage of qualified cybersecurity professionals.”
He adds: “Internal security professionals understand our business and work very closely together with our employees and business partners, whereas our external partners monitor and keep our technology secure. We believe that a mix of internal and external experts keeps us one step ahead of the rapidly evolving cybersecurity threats and technologies.”
A Holistic Approach
An effective cybersecurity strategy means the right mix of people, technology, training and policy, with deficiencies in any of those four pillars constituting a weakness that may be exploited.
For example, even a sophisticated firewall can be breached by determined hackers, so companies should also practice system segregation whenever possible, as well as full data encryption. Again, even those measures can be undone by a stray password, so it is important to keep control of encryption keys.
Meanwhile, physical security should be maintained by controlling access to critical IT infrastructure and restricting the use of USB and other external devices in places such as data centers. Furthermore, use of mobile devices should be monitored and controlled, while the cybersecurity of suppliers should also be assessed, as malware can be embedded in devices or newly made components coming out of the factory.
Another tool in the fight against cybercriminals—albeit one that is also used by them—is artificial intelligence (AI), which can detect probes of data that often precede an attack. “When an attacker breaches an organization, they typically begin gathering as much intel as possible,” Morales notes. “This includes identifying key stakeholders for phishing and spearphishing attacks. Using machine learning allows for the automation of this discovery phase and speeds up the process. The information gathered is then used in a tailored attack against the organization, often leveraging logos and familiar addresses to increase legitimacy.”
To counter such threats, GA Telesis uses tools that leverage AI to predictively analyze threats and new tactics, information it then shares with the wider cybersecurity community.
An Evolving Threat
One of the main challenges of cybersecurity in any business is keeping pace with developments in the strategy of cybercriminals, developments that can quickly render obsolete once-sophisticated countermeasures and even the skills of competent IT staff.
“We have found that the biggest error an organization can make in this era of information security is not the incorrect selection of tools or policy, but rather failing to keep pace with the evolving strategy of cybercrime networks,” Morales says. “We employ continuous improvement to adapt to these shifts quickly and efficiently. As attacks become more complex, so should your defense.”
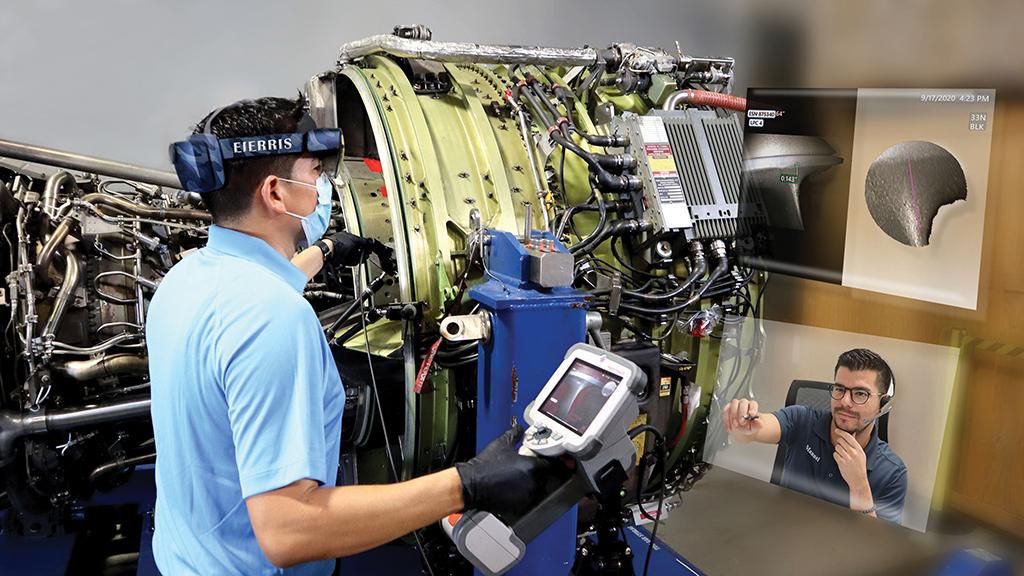
However, this does raise the question of how far the cyber arms race will go, especially as MRO provision becomes more automated, data-led predictive maintenance more important and remote monitoring and working more common. Consequently, the efficiencies gained in these areas might be somewhat offset by the extra information-security investments needed to protect them. Nonetheless, the magnitude of the threat—to a company’s finances, relationships and intellectual property—is such that MRO providers will need to continue their cybersecurity investments in earnest, crisis or no crisis.





